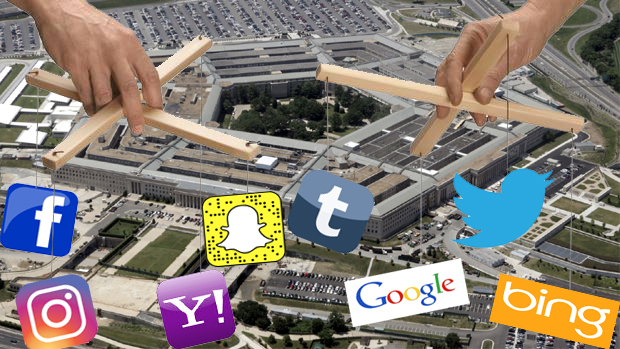
Buried on the very last page of a draft document released last month by a somewhat obscure Pentagon research and development agency, the Combating Terrorism Technical Support Office (CTTSO) describes a technology that may soon join US spy agencies’ online arsenal: a social media mimicry tool that can effectively pretend to be Facebook, Twitter, SnapChat, Instagram, or Tumblr, along with search engines and possibly other sites or applications.
The envisioned technology is described as “a training solution that replicates real-world social media (SM) to avoid the challenges associated with training on the open Internet.”
This doppleganger social media tool, called “Dynamic Social Media for Training and Exercises” (DSMTE), appears to remain an as-of-yet unrealized dream. Patrick Tucker of Defense One describes the document that refers to it, a draft of the annual “Broad Agency Announcement” released by the CTTSO, as “a sort of wishlist of futuristic superhero tools.”
Of the DSMTE tool, Tucker writes:
The Defense Department, State Department, and a variety of partners around the world are constantly working to counter extremist messaging and recruiting on networks like Twitter and Facebook. But these operations carry risks. As author and scholar J.M. Berger has observed, the State Department can’t just pick a fight with a random jihadist or ISIS supporter on Twitter: “You have a lot of people watching to see if you’re going to lose the argument.” Such exchanges are all upside for the radical, all downside for the establishment.
Like every military action, psychological operations on social media require training. The Pentagon is looking for a virtual social media site trainer called the Dynamic Social Media for Training and Exercises, which can emulate the look, feel and the key features of Facebook, Twitter, Snapchat, Instagram and Tumblr, to support “operator collection, analysis and exploitation of social media during training and exercise” while avoiding “the challenges associated with training on the open Internet.”
Of all the challenges that counter terrorism operators face, “the open Internet” seems relatively benign.
While the government certainly seems to want to avoid conducting its online psychological operations too obviously, and may not have its ideal fake version of Facebook and other sites up and running yet, it has certainly been training, at the very least, for the kind of ops that it feels could be further enabled by the proposed DSMTE tool.
A report from earlier this year, for example, outlined an intricate training exercise in which sophisticated “personas” were fabricated for use in social media ops “with identified knowledge objectives, belief objectives, and desired outcomes using psychological theory as a framework for message development.”
Other attempts and ideas floated within US intelligence and counter-terrorism circles as ways to artificially engineer the terrain of the cyberspace battlefield include algorithms to automatically censor social media or to use it to predict future terrorist attacks. The FBI, which is known to have used fake websites and internet personas in online investigations in the past, has recently been given the green light to impersonate journalists in some circumstances. The bureau also recently received unprecedented new hacking powers. Another new proposal that I recently wrote about, which boils down to using chatbots to troll suspected ISIS sympathizers, adds to this collection of prospective plans for how to stop the terrorists from taking advantage of the internet.
Last month’s CTTSO draft document suggests that the Pentagon’s fake multi-use social media platform is at this point still nothing more than an idea looking for a contractor to make it a reality. The DSMTE, which “must also provide a realistic web-search capability (e.g. Google, Bing, or Yahoo) with integrated web crawlers that allows for the conduct of internet searches which will return realistic search results” will only be used for training purposes, we’re told.
“At the conclusion of the contract,” however, “all equipment and software required to run and support the DSMTE shall be transitioned to the Government.” Whether the government then uses its imitation internet environment for purposes other than training — such as for targeting individuals for intricately engineered psychological operations based on personally tailored disinformation appearing to generate from search engines or from the target’s social media contacts, for example — and whether such activities, if they occur, will be disclosed to the public, will from then on remain the government’s prerogative, of course.

Help keep independent journalism alive.
Donate today to support MirrorWilderness.com.
$1.00

One thought on “Pentagon wants capability to mimic social media sites, search engines”