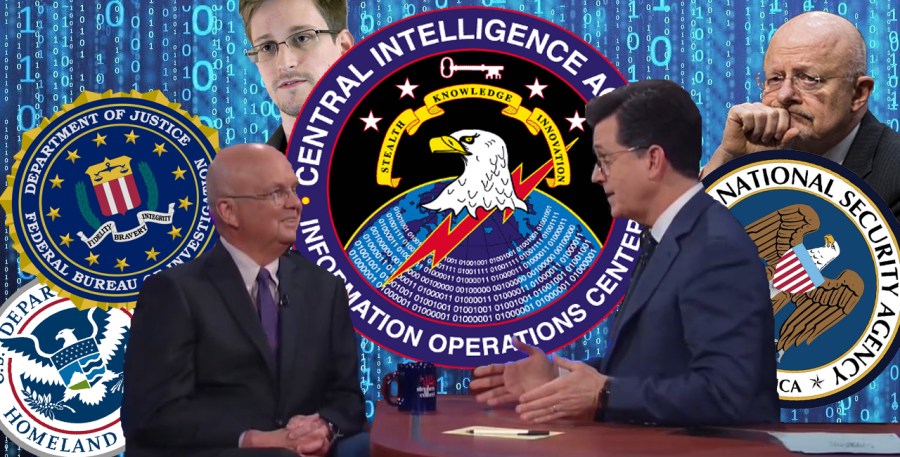
In the wake of Wikileaks’ bombshell “Year Zero” disclosures on Tuesday, former Central Intelligence Agency and National Security Agency Director Michael Hayden, a frequent defacto spokesman for the intelligence establishment, appeared on the Late Show with Stephen Colbert, of all places, to awkwardly attempt to explain the stunning revelations.
Hayden cracked a joke or two during the interview. He said that President Donald Trump “seemed to have forgotten that he was the president of the United States” when he tweeted over the weekend that President Barack Obama had tapped his phones at Trump Tower.
Yet it was also painfully obvious that Hayden’s appearance in the setting of a comedy show like Colbert’s was a public relations move, an attempt at damage control to distract from the seriousness of the Wikileaks revelations — which amount to the “smoking gun” confirming people’s worst suspicions about the extent to which the government can hack into just about any device or operating system and turn things like phones and even TVs into covert “bugs” for surveillance. Given the gravity of the Wikileaks documents, it was inconceivable that Hayden wouldn’t be asked about it.
“Weeping Angel is the name of the program where they’re looking through my TV,” Colbert said. “Is the CIA listening to me through my microwave oven and through my TV and through my cell phone? Are they doing that sir?”
“No,” Hayden responded.
“If they were, would you say yes?” Colbert asked.
“Yes,” Hayden said.
“Is that a true answer?”
“Yes, look –”
“I don’t believe you,” Colbert said.
“I get that a lot,” Hayden said. At this point Hayden was openly laughing at his own responses to the questions while Colbert was trying not to laugh. Hayden recovered to some extent from the exchange, returning to an earlier argument he’d been making that focused on the notion that the CIA’s hacking capabilities are never used on law-abiding Americans and that there is a functional system of accountability governing their use.
Yet the more we learn about the day-to-day activities of the intelligence community through leaks, Freedom of Information Act lawsuits and investigative reporting, the less plausible this line of argument becomes. In its press release regarding the “Year Zero” installment of its “Vault 7” release on Tuesday, Wikileaks noted that the set of documents it was publishing not only “gives its possessor the entire hacking capacity of the CIA” but that it “appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.”
This allegation that detailed information on the CIA’s hacking capabilities circulated freely without authorization is reminiscent of claims by Edward Snowden, the whistle blower who leaked documents exposing many of the NSA’s surveillance programs in 2013.
“I, sitting at my desk, certainly had the authorities to wiretap anyone, from you, or your accountant, to a federal judge, to even the President if I had a personal email,” Snowden said at the time. Subsequently, much of the narrative put forth by the NSA about the Snowden revelations focused on the supposed accountability built into the system and embodied in the secretive Foreign Intelligence Surveillance Act (FISA) Court.
Similarly, in the realm of domestic law enforcement and surveillance, federal agencies including the Department of Justice and Department of Homeland Security claimed last year that they do not use sophisticated cell phone surveillance devices known as cell-site simulators (a.k.a. IMSI-catchers or “Stingrays”) to do anything but track phone locations. More recent reporting, however, has revealed that guidelines are much looser at the state and local level, allowing police around the country to use technologies that can remotely capture virtually any data on a smart phone, including things like text messages and photos and even deleted information.
Given that federal law enforcement agencies like the DHS and DOJ have bigger fish to fry than local cops, it makes sense that they would have stringent guidelines about their own uses of surveillance technology. It is not that hard to get a warrant for someone already genuinely suspected of terrorism or whose name is on the FBI’s most wanted list. Yet if the feds want the goods on lower level targets, it seems there would be few obstacles preventing them from soliciting that information from local law enforcement. That is what fusion centers are for, after all.
It is well-established, however, that local police have been caught abusing their access to confidential data. Hundreds of local law enforcement officers, in fact, have been fired, suspended, or resigned in recent years over misuse of databases to which they had access. And there is no reason to think the problem disappears as one ascends the governmental hierarchy.
“Over the last three years the United States intelligence sector, which consists of government agencies such as the CIA and NSA and their contractors, such as Booz Allan (sic) Hamilton, has been subject to unprecedented series of data exfiltrations by its own workers,” Wikileaks notes in its “Year Zero” press release.
The transparency advocacy group notes that the most recent high-profile case of a federal employee getting caught abusing their access was that of Harold T. Martin III, who was arrested last year and last month was indicted with 20 counts of mishandling classified information, but that there are others. “A number of intelligence community members not yet publicly named have been arrested or subject to federal criminal investigations in separate incidents,” according to Wikileaks.
The CIA, the NSA, and the broader U.S. intelligence community can trot out their cheerleaders on as many talk shows as they want to, and try to spin the existence of the shadowy FISA Court and a congressional oversight committee that isn’t even allowed to know how many Americans the government spies on into some kind of robust system of checks and balances that does an effective job at keeping America’s spying apparatus in line. But at the end of the day, the U.S. government’s cover story that its incredible surveillance capabilities are never abused is wearing thin.

Help keep independent journalism alive.
Donate today to support MirrorWilderness.com.
$1.00
