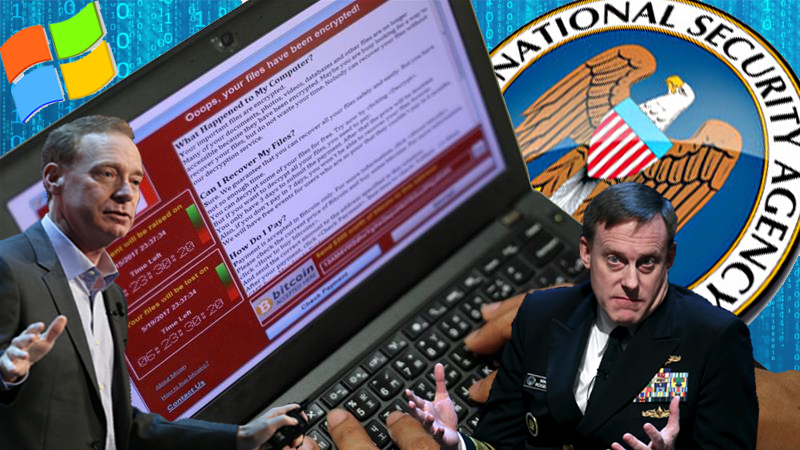
Last week’s cyberattack on computers in multiple countries via ransomware known as “WannaCry” has made numerous headlines and sparked much discussion and criticism. One side of the story of this major security breach to receive less attention, however, is the light it shines on the cozy relationship between major tech companies and the National Security Agency.
It is unclear at this point who was behind the reportedly somewhat amateurish deployment of the WannaCry virus (also known as WCry or WannaCrypt) on May 12, though some have suggested it was North Korea. Regardless of which state actor or rogue group of hackers is responsible for using the ransomware, though, critics have been quick to point out that WannaCry conspicuously utilizes an exploit called EternalBlue, which targets Microsoft Windows and originated at the NSA. EternalBlue was exposed last month by the Shadow Brokers, a sketchy hacking group that gained notoriety last summer for publishing numerous NSA hacking exploits.
As always, attribution is difficult, but unlike some other recent breaches, it appears fairly unlikely that Russia is behind this one. Computers in Russia were apparently hit disproportionately by WannaCry, and Russian President Vladimir Putin has denied his government’s involvement in unleashing the virus.
“We are fully aware that the genies, in particular, those created by secret services, may harm their own authors and creators, should they be let out of the bottle,” Putin reportedly said following the cyberattack. He also mentioned Microsoft’s involvement.
“With regard to the source of these threats, then I believe that Microsoft has spoken directly about this,” Putin reportedly said. “They said that the first sources of this virus were the United States intelligence agencies. Russia has absolutely nothing to do with this.”
Indeed, Microsoft’s president and chief legal officer Brad Smith responded to the WCry cyberattack with a blog post aggressively pointing the finger at the NSA, in which he described the ransomware attack as a “wake-up call for all of us” that “provides yet another example of why the stockpiling of vulnerabilities by governments is such a problem.”
“This is an emerging pattern in 2017,” Smith’s post continues. “We have seen vulnerabilities stored by the CIA show up on WikiLeaks, and now this vulnerability stolen from the NSA has affected customers around the world. Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage. An equivalent scenario with conventional weapons would be the U.S. military having some of its Tomahawk missiles stolen. And this most recent attack represents a completely unintended but disconcerting link between the two most serious forms of cybersecurity threats in the world today – nation-state action and organized criminal action.”
Yet there is another disconcerting link between two important categories — those of entities responsible for safeguarding against cybersecurity threats — that Smith seems to gloss over. That is the intimate connection between the NSA and US-based private tech companies. While Microsoft might prefer to cast the NSA as the bad guy for its own public relations reasons, though, there are good reasons for the public to suspect they may have known about the exploit before releasing a patch to their product following the publication of EternalBlue.
“That nobody else discovered these vulnerabilities as far as we know suggests that it is right for the NSA to hold onto them if they have confidence that nobody else has a copy of their tools,” University of California Berkeley researcher Nicholas Weaver reportedly said following the WCry attack. “It actually is a problem that the NSA can’t or won’t claim credit for properly notifying Microsoft,” Weaver added, somewhat tellingly. “The NSA did the right thing, and they aren’t getting the credit for it they deserve.”
Indeed, with all of the anger and paranoia that is frequently directed at the NSA, the complicity of private tech companies is often overlooked in the surveillance debate.
Whether it was Microsoft, Google or the other companies involved that denied knowledge of the NSA’s PRISM data collection program in 2013, or Apple during its highly-publicized (and ridiculous) fight last year with the FBI over unlocking a terrorist’s phone, or Facebook with its recent shift from calling election influence campaigns using fake accounts “a pretty crazy idea” to releasing a report loaded with intelligence agency-style jargon on “information operations” on its platform, though, the cooperation of these major tech companies is apparent and lacking in plausible deniability.
The NSA certainly has egg on its face, once again, following the WannaCry ransomware attack. Yet even as the agency’s failure to protect its exploits underscores its fallibility, the shared burden of responsibility of private sector firms for these security failures is also exposed. For all the lip service they pay following an embarrassing incident, the major tech companies appear to largely continue to unquestioningly comply with the government’s surveillance requests. As long as they continue to do so, such awkward moments of finger pointing and denial by the tech companies’ respective PR departments will continue to periodically emerge.

Help keep independent journalism alive.
Donate today to support MirrorWilderness.com.
$1.00
